Author: IbukunOluwa
Leadership Lessons Series – Letter “D”
The leadership/human competency “Directedness” encompasses many traits Direct? To lead those who look up to us with sincerity, integrity, honesty and genuity. Being direct as a leader requires a strong moral compass, and the courage to conduct oneself with integrity regardless of the potential personal cost. Directness does not translate to rudeness, rather to the character and competence to speak the truth to all, without fear of consequences or favor in selecting those we choose to be honest with. Direct leaders blend tactfulness with candidness to serve the best interests of their charges and all. Follow the Ladder Back Down on LinkedIn and YouTube.
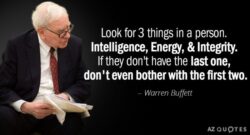
Integrity Matters
The most crucial value in a leader, employee, employer and any human being is integrity and Warren Buffet was right when he said “You’re looking for three things, generally, in a person, intelligence, energy, and integrity; and if they don’t have the last one, don’t even bother with the first two. For this reason, the sole #examsgrade I have posted – and will ever post – on my LinkedIn profile from my #education and #qualifications journey is my GRADE A from The Chartered Institute for Securities & Investment (The CISI) #integritymatters #ethics and #integrity test which I sat in 2014. I can proudly say that’s my greatest academic accomplishment ever, & a resounding message to any employer that may consider hiring me, that I am flexible regarding most things, with the exception of my personal #integrity, #values and #ethics which extends beyond any corporate #valuesstatement or #codeofconduct I may be required to sign. Integrity may not pay in kind, but it does pay with time. Everyone truly has a price as they say. Mine? A solid five to six hours sleep at night without having to fret over what #ethical compromises I may have made during the daytime. #integritymatters #GradeA #ethicalleadership
The $2 Trillion Dollar Cyber Crime Industry and the Corporate Board’s Fiduciary Responsibilities
With Operational Resilience scoring high on the agenda of global regulators, boards need to consider regulatory expectations requiring the engagement of Chief Information Security Officers and CIOs in the the board room. Why are CIOs/CISOs still struggling to get a seat at the table? Not because board CIOs/CISOs aren’t speaking ‘strategy’ language – as is often suggested; rather because many boards aren’t aware of the CIO/CISO’s capability to help board directors fulfil their fiduciary duty to “protect corporate assets from both internal and external loss and fraud”. In most instances, obtaining or destroying valuable ‘information assets‘ is the goal of the internal or external cybercriminal, with the proceeds of money laundering, fraud, theft of intellectual property, blackmail, and ransomware emboldening global cyber criminals who continue to seek wealth at all costs. Negligence that results in the theft or loss of information assets – including intellectual property, personal customer data, patents etc. – is an act that could render the Board in breach of their ‘fiduciary duty of care’. With the GDPR and the Data Protection Act 2018 having come into force May 2018, the case for having a CIO/CISO on the board (who not only understands the fiduciary responsibilities of the Board s/he has been appointed to join, but who speaks both technical and business language), has never been stronger. The risk of cyber and information security breaches needs to be recorded as ‘high’ on the corporate risk register – rather than just on the IT or Cyber department’s risk register – with the Board having visibility into these risks, approving the controls needed to mitigate these, and retaining an ongoing oversight of these risks. Quantifiable cybercrime attacks against organisations are becoming more prevalent, e.g. ‘CEO email fraud’ or whaling attacks, with the biggest reported victim, i.e. ‘Crelan Bank’ having lost $76 million to the fraud in 2016. Another victim, FACC, lost €52.8m to a similar fraud. Last week, it was reported that the CEO of Barclays, Jes Staley, fell victim to a spoofed email sent from a disgruntled customer, which thankfully didn’t result in monetary loss to the bank. By now, Board executives should be asking “is simply ‘sacking the CEO, CIO, CFO or CISO after a Cyber breach a prudent response to Cyber and Information Security breaches?”. Instead of sacking the perceived ‘culprit’ after a breach has occurred – including cyber security breaches as a high risk on the corporate risk register, discussing these at board meetings, and gaining assurance from the CIO or CISO that adequate controls are in place to mitigate against the risk of such breaches actually taking place may be a better approach. Sacking executives after a breach, rather than seeking to prevent a breach in the first instance, is merely reactive; whereas the latter approach of prudent risk management is proactive and seeks to empower the board to fulfil its obligation to protect corporate information assets. Many controls are available that could help to mitigate information and Cyber security risks and empower the Board to protect corporate information assets, including people, technology and operational controls. Operational Culture Encourage staff to speak up without fear. Many ‘process, technical and human risks’ tend to be spotted by front-line employees who deal with customers each day (or who use information systems regularly), long before the risk materialises into an issue. A seemingly ‘disgruntled’ junior Fintech employee who ‘grumbles’ among their peers about a manager ‘posting large remittances through the finance system to a Cleaning firm’ may be alerting their peers to ‘procurement fraud’ or ‘money laundering’. If there’s a culture of fear over raising concerns to leadership, the employee will continue to complain to peers who don’t have the power to protect the firm’s assets from fraud or loss; whereas the Board has both the power to do so – in addition to a legal obligation to do so. Since the Board is responsible for setting the corporate culture it truly wants to see – employees must be encouraged to speak out in the interest of the firm and shareholders, without fear of victimisation or harassment for doing so; in particular as an employee speaking out against potential fraud is empowering board members to fulfil their fiduciary responsibility of care and protection of the firm’s assets – including non-financial assets. Processes A Board must ensure the separation of duties and conflict of interest rules are followed to the letter. If the CEO is only allowed to sign off on $50m transactions, then adequate workflow controls could be implemented to cap this limit, and to flag an alert each time the limit is reached (whether this limit is reached in one transaction – or over a series of transactions to a single firm in a short space of time). In addition, the CFO shouldn’t be fearful of asking questions of the CEO if asked to make financial remittances that seem amiss. The CFO could be saving both his and the CEO’s job, as well as helping the Board to protect the firm’s assets from cybercriminals. Board Development CIOs/CISOs are well-placed to run cyber security awareness training for the Board and Senior Management team, including training in the risk of Phishing, Whaling, and Ransomware. The landscape for information security threats has changed drastically, with ‘Crime-as-a-Service’ raking in billions of dollars a year for Cybercriminals. When Boards become as desperate to protect a firm’s information assets, as cybercriminals are to defraud companies of the same assets, the balance will cease to be tipped in the cybercriminals’ favor. Technology Countless technology tools exist to help protect against cybercriminals – including auditing, alerts, and network security tools; and a basic act of providing internal and external board members – i.e. including the Chair – with an internal email address and then configuring the email server to change all internal emails sent from each board member and each C-level exec. to each other to – say – ‘Brown font’ could help. If a spoofed email were to arrive with a different colour font, purportedly from the Chair to the CEO, the different colour font could flag a warning in the mind of the CEO to ring the Chair to double-check on the origin of the email. Conclusion For board members to successfully fulfil their fiduciary duties, discussions at Board meetings should include Cyber and information security risks, including the risk of C-level execs. falling prey to cybercriminals. Failing to do so could cause significant loss of financial assets, plus market value or share in a corporation, in some instances resulting in insolvency. Essentially, any strategic risk that can cause a loss of assets, reputation or shareholder value to the firm must be discussed at the table by the board, and those discussions should be held with CIOs and CISOs present – many of whom are able and ready to contribute as a strategic board member, thereby empowering the board to fulfil its fiduciary duties to the company, its employees, and regulators. Ibukun Emmanuel-Adebayo
The Big Risks of Your Tiny USB Stick
So you’ve been handed a brand ‘new’ USB (Memory) stick at a conference, or you’ve found a misplaced USB stick on the floor inside or outside the office, and you want to find out what’s on it – so you can return it to its rightful owner; what’s the first thing you do with the stick? Most PC users assume the innocence of the tiny and yet durable USB stick; and therefore plug any USB stick they lay their hands upon into their work or home PC, with the belief the stick is malware and virus-free; an assumption that can cause a huge cyber-security breach on your network or PC. One of the first notable viruses to hit the news in the late 1990’s was the Melissa virus followed promptly by the Nimda and I Love You Worms, which spread rapidly across global networks. Some of these names may sound alien to new professionals whereas – for those of us involved with IT as a user or professional – since the year 2000 – these outbreaks probably remain ingrained in our memories. The Melissa malware was a virus – rather than a worm – as it didn’t self-propagate (spread) through network shares, having been developed to run in macros in standalone Microsoft Word documents – and therefore largely affected Word users only. On the other hand, similar to more recent threats, Nimda was one of the first worms developed, that used multiple methods – including social engineering i.e. the exploitation of ‘human’ weaknesses to spread – inviting users to click on links to infected websites, or to open infected email attachments. The ‘I love You’ worm also exploited human curiosity – dispatched in an email attachment titled ‘Love letter for you’. Surprisingly, even though this wasn’t sent on Valentine’s day, tens of millions of users were curious enough to click on an attachment from a stranger professing ‘love’; causing a global infection of their PCs. USBs and Social Engineering Have you ever viewed PDF’s titled ‘the top 20 secrets to wealth’, or ‘Please help’, or ‘Strictly private and Confidential’, and decided to take a brief look inside the document? Cybercriminals often use clickbait titles to lure curious users into infecting their PCs with malware from such documents, including on USBs – which are sometimes deliberately dropped on the floor for curious users to pick up and start a viral infection of PCs. USBs aren’t immune to viruses or malware, and yet they’re doled out at conferences like candy; picked up off office floors – or streets – by unsuspecting or curious users as a matter of course, and subsequently plugged into personal devices without a thought for the security of the device or for other network users. So what should Boards, IT, and PC users do, in a bid to mitigate the risk of malware and viruses from being introduced onto the network viz. USBs? “Boards” Continuing along the theme of the Board’s fiduciary responsibility to protect a corporation’s information assets from theft or loss – including the Board Executive’s accountability for the Corporate Cyber and Information Security Policies; it goes without saying that the small USB can cause a massive loss of information assets to a business – in the form of viruses, ransomware and other malware outbreaks. Information leakage, i.e. wherein authorised and unauthorised network users depart unsecured businesses each day, with ‘tiny’ USBs on their person, containing intellectual property – or private customer information – is also a ‘big’ risk that needs to be owned and mitigated by the Board. What happens when an authorised employee misplaces a USB stick containing personal customer data – or leaves it on a train, and fails to report this? “IT/Infosec Leaders” At this level, we should be overseeing our teams’ cyber risk management initiatives such as DLP solutions, patch management, plus anti-malware and anti-virus solutions – ensuring our firm only purchases encrypted USBs that can also be remotely wiped in the event of theft or loss; plus we also need to oversee the blocking of all unencrypted USB sticks from the network, using GPO or other third party solutions. Has your team been provided with adequate testing facilities, including a ‘safe’ standalone machine to test potentially suspect USBs and software on? How about the asset inventory system containing details of each IT asset, including USBs, on the network? Is this updated (and reconciled) periodically? We should also be iteratively raising user awareness through policies, workshops, training, bulletins, competitions etc., i.e. every effort has to be thrown towards reducing the threat of information asset theft and cybersecurity henceforth, not only due to the impending GDPR, but also if we’re intent on thwarting the Cybercrime industry from morphing into a $2Trillion dollar industry by 2019, at our personal workplaces’ expense. “Users” Again, as I wrote on LinkedIn previously, Information Security is the responsibility of all staff, and it’s thus vital we individually take up the mantle of protecting our workplace and personal PCs from harm. Before you plug that USB or memory stick into your personal computer, pause and think – ‘what if?’; i.e. ‘what if this stick contains a virus or a worm on it?’; ‘what if this were to delete all my information on my PC – along with my entire work data?’; ‘what if this were to affect the office network for a day or two – could we continue as a business?’; ‘ what if this stick contains malware that could transmit all my stored personal information, or keystrokes I type on my PC, to a remote device – including financial information?’ (such software has existed for years). If you’re given a USB stick by a friend, colleague or at a conference – ensure it’s scanned through an antivirus and anti malware software before you use it! If you notice a USB stick lying on the streets – just keep walking – let the owner return to find it where they dropped it – accidentally or maliciously! “Conclusion” Whilst memories or knowledge of the old viruses and malware may have diminished, the modern day cybercriminal has become more emboldened, using various methods, including the USB stick, to distribute their potent payload – exploiting not just software vulnerabilities – but largely human vulnerabilities, including unawareness and curiosity. Even if you don’t remember Melissa, Nimda, or I love you; the more recent malware outbreaks are enough to let people know that those pesky Cybercriminals aren’t playing a game – it’s big business for them. Don’t inadvertently contribute to the thriving Cybercriminal industry, including as a victim – even if you have to forfeit some love from Melissa. Comments welcome!
Sample Third-Party Cyber Risk – Self-Assessment (Questionnaire)
Since delivering the Third-Party Vendor Cyber Risk Assessment workshop earlier in the year, I’ve been inundated with requests for the sample questionnaire I used for the session. A copy of the *sample questionnaire is enclosed at the end of this post, and here’s a process a Cyber Analyst may undertake in the workplace to complete a third-party vendor cyber risk assessment using a similar questionnaire: the spreadsheet would be sent to a third-party vendor for them to assess and score themselves (i.e. a self-assessment) in column A of the worksheet named ‘Questionnaire’. the ‘Scorings’, ‘Bar chart’ (and/or newly added ‘Radar chart’) worksheets would be hidden from the vendor’s view but the scorings would be automatically populated as the vendor completes their self-assessment. Once completed and returned by the vendor, the IT or InfoSec Analyst would: unhide all hidden worksheet(s) analyse each risk score against their company’s risk tolerances e.g. under the ‘Accreditation and Compliance’ cell A103, the sample company has scored 75% as they are not ISO 27001 accredited (0 score in cell A99); if the Analyst’s company only works with vendors accredited to ISO 27001 standards, the question needs to be raised as to whether this vendor is within tolerance (despite being accredited to Cyber-Essentials and PCI-DSS standards). ask for further information from the third-party vendor if required (including evidence to back up the scorings). Note that some firms may decline to provide copies of their private internal policies, procedures pen-test reports etc., and may only provide selective evidence such as SOC2 Reports, summary external audit reports and evidential notes of ongoing/completed remediation work on audit findings. advise internal stakeholders and provide them with critical guidance to reach an informed decision on whether to onboard the third-party vendor or not (the risk owner may essentially choose to accept the risk posed by the vendor’s lack of ISO27001 accreditation in lieu of other accreditations held and other risk ratings in the self-assessment overall); do not take any risk decisions taken against your professional advise personally as it’s not about you or I – it’s about the business!!! If assurance is being sought from a critical vendor providing essential applications, systems, processes or services to the business, repeated assurance could be sought annually with a subset of these questions asked each time to ensure the company’s cybersecurity risk controls remain within the tolerance set by your company’s senior management team or board. *Most companies will have their own questionnaires or alternative processes, systems or tools to seek assurance their third-party vendors (and increasingly fourth-parties) have adopted and are maintaining effective Cybersecurity and IT risk management controls; this questionnaire is purely an example of some questions a company may choose to ask vendors. Good practice dictates that each firm should tailor and send out questionnaires that are commensurate to the services being procured, and in accordance to the risk that each third-party might pose to its information assets and privacy obligations. Finally, a self-assessment questionnaire is one of many tools used to comply with our due diligence obligations as cybersecurity professionals, to ensure we only onboard third-party vendors who provide the same degree of protection to our clients’, employees and company’s information assets as we do. Also, do remember we may also be required to complete due-diligence questionnaires (DDQ’s) on behalf of our organisation for companies we may provide services to. Download the read-only sample questionnaire below and please feel free to contact/connect with me through my LinkedIn profile with any questions. Sample Third-Party Vendor’s Self-Assessment-Questionnaire – Cyber Risk Scoring Follow the Ladder Back Down on LinkedIn and subscribe to us on YouTube.
Low-Cost Compliance
With compliance still high on the regulatory agenda of many firms, how can corporate leaders ensure employees continue to practice the documented business ethics? Walk the ethics walk – by example – and keep walking it. Practically demonstrate higher standards than expected of employees Establish a zero-tolerance environment for dishonesty Encourage employees to ask questions Do only what you would accept from the general workforce. Write ethical conduct into role profiles and evaluate and reward honest conduct, annually Implement an unbiased and genuine whistleblowing policy and helpline Review and act upon exit interview notes of departing employees Examine online employer review sites to find out what employees are too scared to tell their managers Be transparent. A transparent organisation is a compliant organisation None of the above tips cost as much as having to pay regulatory, legal or associated costs for a compliance policy that is documented, but practised on ink and paper only. Compliance does not have to cost much more than decisive visible leadership action.
Leadership Lessons Series – Letter “D”
The leadership/human competency “Directedness” encompasses many traits Direct? To lead those who look up to us with sincerity, integrity, honesty and genuity. Being direct as a leader requires a strong moral compass, and the courage to conduct oneself with integrity regardless of the potential personal cost. Directness does not translate to rudeness, rather to the character and competence to speak the truth to all, without fear of consequences or favor in selecting those we choose to be honest with. Direct leaders blend tactfulness with candidness to serve the best interests of their charges and all. Follow the Ladder Back Down on LinkedIn and YouTube.
Integrity Matters
The most crucial value in a leader, employee, employer and any human being is integrity and Warren Buffet was right when he said “You’re looking for three things, generally, in a person, intelligence, energy, and integrity; and if they don’t have the last one, don’t even bother with the first two. For this reason, the sole #examsgrade I have posted – and will ever post – on my LinkedIn profile from my #education and #qualifications journey is my GRADE A from The Chartered Institute for Securities & Investment (The CISI) #integritymatters #ethics and #integrity test which I sat in 2014. I can proudly say that’s my greatest academic accomplishment ever, & a resounding message to any employer that may consider hiring me, that I am flexible regarding most things, with the exception of my personal #integrity, #values and #ethics which extends beyond any corporate #valuesstatement or #codeofconduct I may be required to sign. Integrity may not pay in kind, but it does pay with time. Everyone truly has a price as they say. Mine? A solid five to six hours sleep at night without having to fret over what #ethical compromises I may have made during the daytime. #integritymatters #GradeA #ethicalleadership
- 1
- 2